CWE & CAPEC Definitions
CVEFeed.io includes a built-in knowledge base of CWE (Common Weakness Enumeration) and CAPEC (Common Attack Pattern Enumeration and Classification) definitions. These are MITRE frameworks that help you understand why a vulnerability exists and how an attacker might exploit it — going beyond just knowing that a CVE was published.
- CWE classifies the underlying software or hardware weakness behind a vulnerability. For example, CWE-89 is “SQL Injection” and CWE-79 is “Cross-Site Scripting”. When you see a CVE linked to a CWE, you immediately know the category of flaw and can apply the right class of fix.
- CAPEC describes common attack patterns — the techniques and approaches adversaries use to exploit those weaknesses. For example, CAPEC-66 describes “SQL Injection” as an attack pattern with its prerequisites, required skills, severity, and likelihood of attack.
Both are accessible from the Knowledge Base section in the sidebar.
CWE — Common Weakness Enumeration
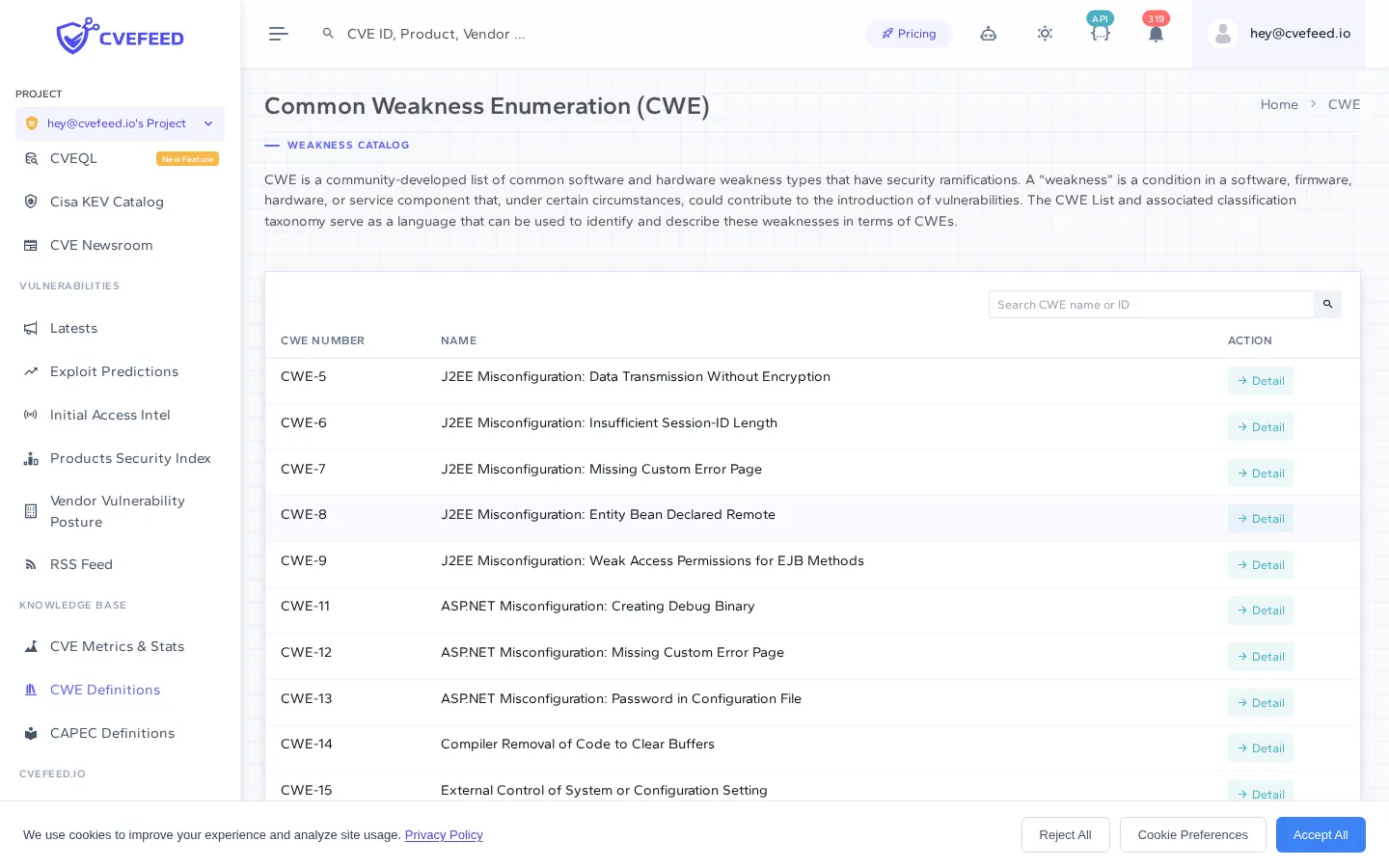
Browsing CWEs
The CWE index page lists all weakness definitions in a searchable, paginated table. You can search by CWE number (e.g., “79” or “CWE-79”) or by name (e.g., “injection”).
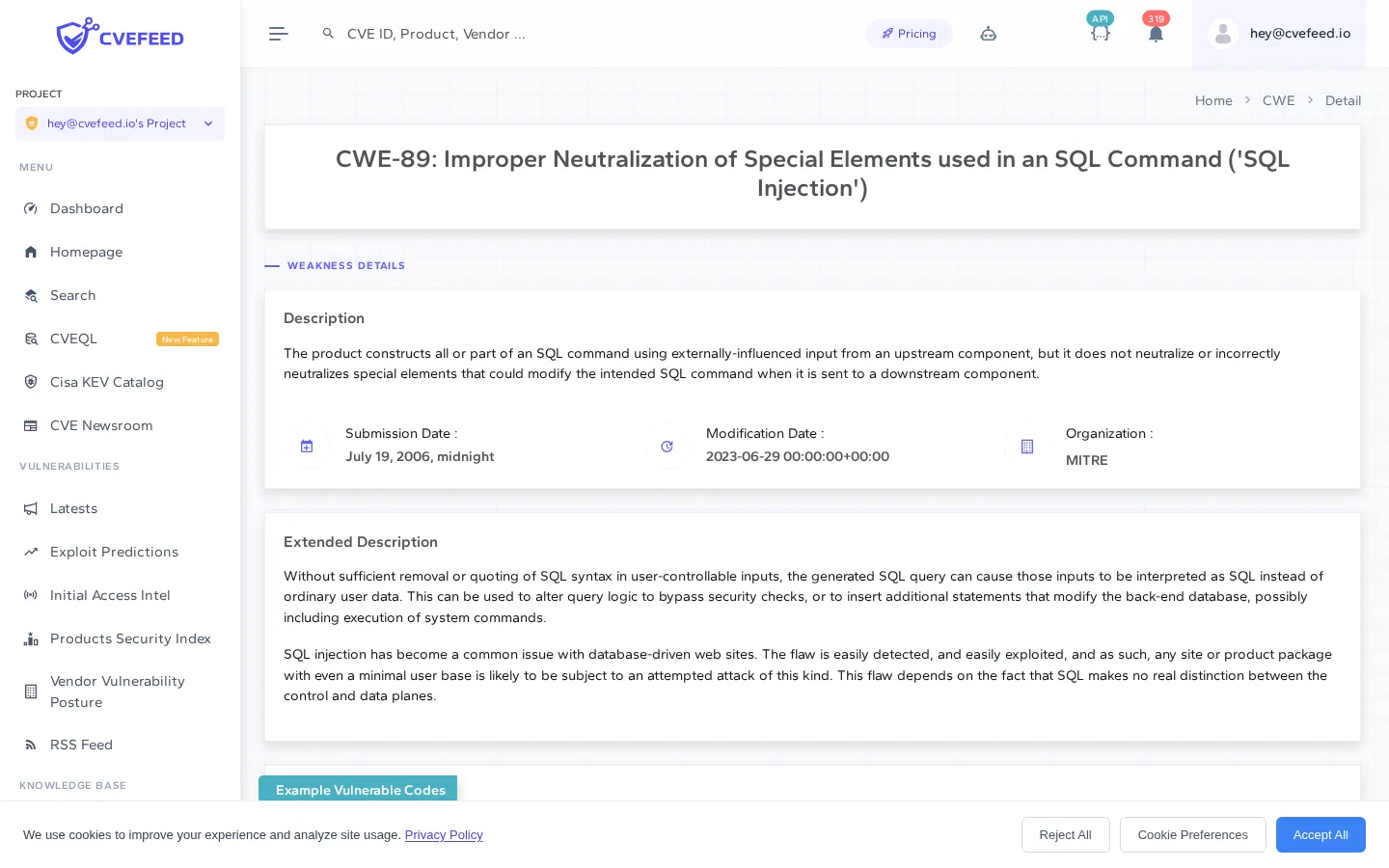
CWE Detail Page
Click any CWE to open its detail page, which includes:
- Description — what the weakness is and how it manifests.
- Extended description — in-depth explanation of the weakness, including how it occurs and its potential impact.
- Example vulnerable code — demonstrative code snippets showing how the weakness appears in practice, with syntax highlighting.
- Related weaknesses — links to related CWEs at higher and lower levels of abstraction, helping you understand the weakness hierarchy.
- Submission and modification dates — when the CWE was first cataloged and last updated.
CAPEC — Common Attack Pattern Enumeration
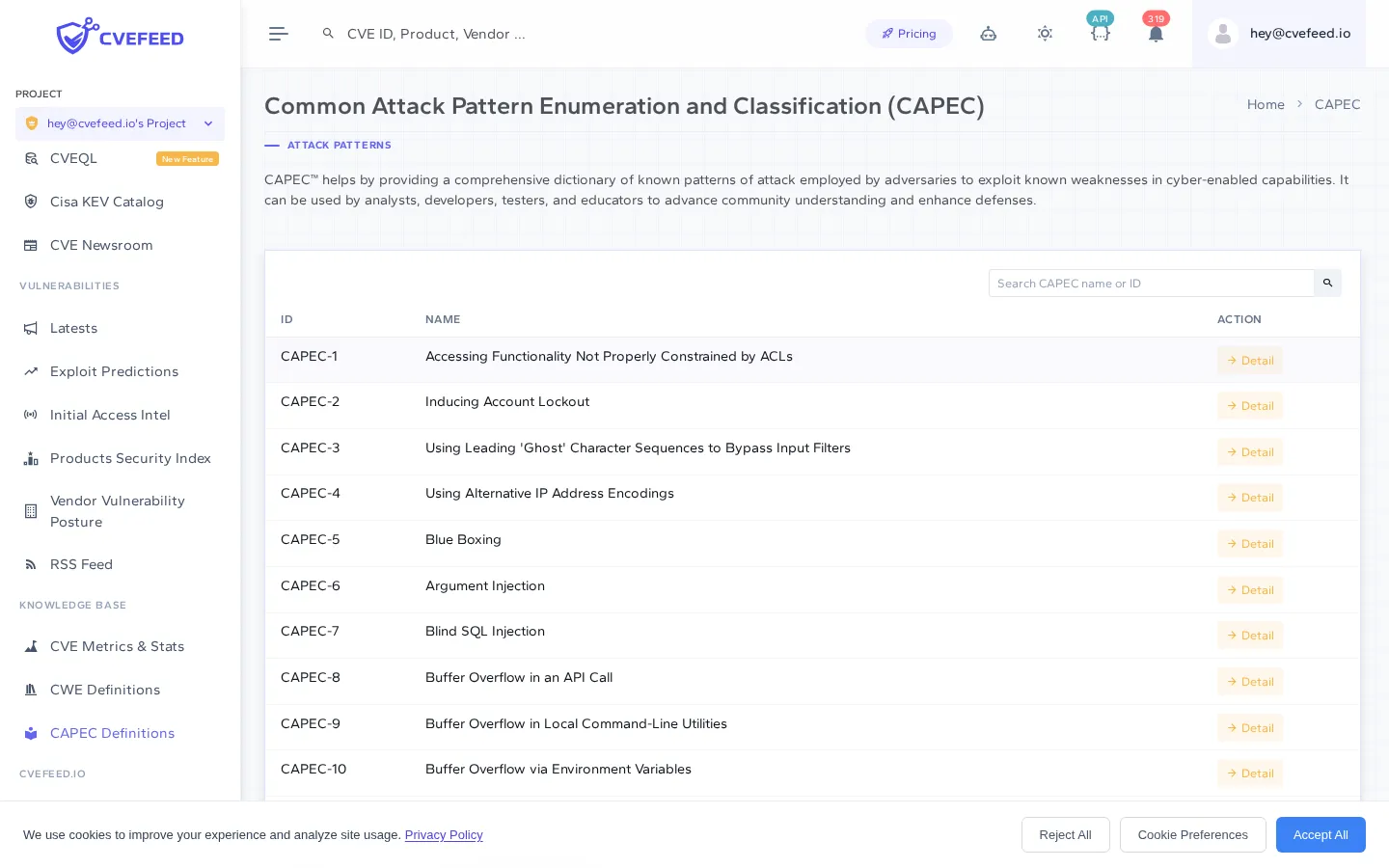
Browsing CAPECs
The CAPEC index page lists all attack pattern definitions in a searchable, paginated table. Search by CAPEC number (e.g., “66” or “CAPEC-66”) or by name (e.g., “buffer overflow”).
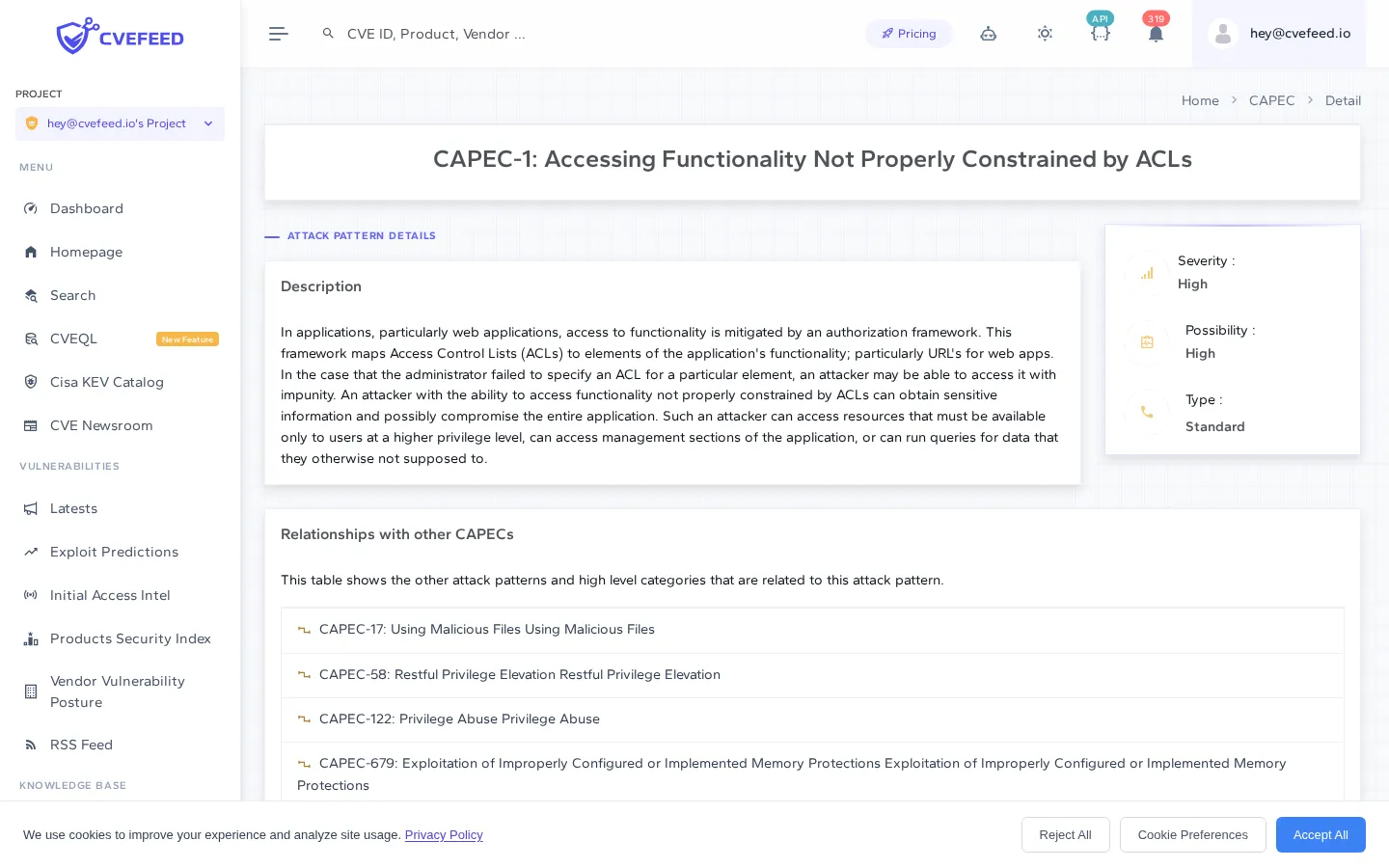
CAPEC Detail Page
Click any CAPEC to open its detail page, which provides a comprehensive view of the attack pattern:
- Description — what the attack pattern is and how it works.
- Severity and likelihood — how severe the impact is and how likely the attack is to occur, displayed in the sidebar.
- Abstraction type — whether this is a high-level meta pattern or a detailed, specific technique.
- Prerequisites — conditions that must be met for the attack to be feasible.
- Skills required — the attacker skill level needed, broken down by category with color-coded badges (Low, Medium, High).
- Resources required — what tools or access the attacker needs.
- Related attack patterns — links to related CAPECs.
- Related CWEs — the weaknesses that this attack pattern exploits, with links to their detail pages.
- Taxonomy mappings — cross-references to other frameworks like MITRE ATT&CK, OWASP, and WASC.
Integration with Vulnerability Pages
CWE and CAPEC data is not siloed — it’s integrated directly into CVE detail pages. When viewing any vulnerability:
- The CWE card shows which weaknesses are associated with that CVE, with links to the full CWE detail page.
- The CAPEC card shows which attack patterns are related to those weaknesses, with links to the full CAPEC detail page.
This gives you a complete chain: from a specific vulnerability (CVE), to the type of weakness it represents (CWE), to how an attacker might exploit it (CAPEC).