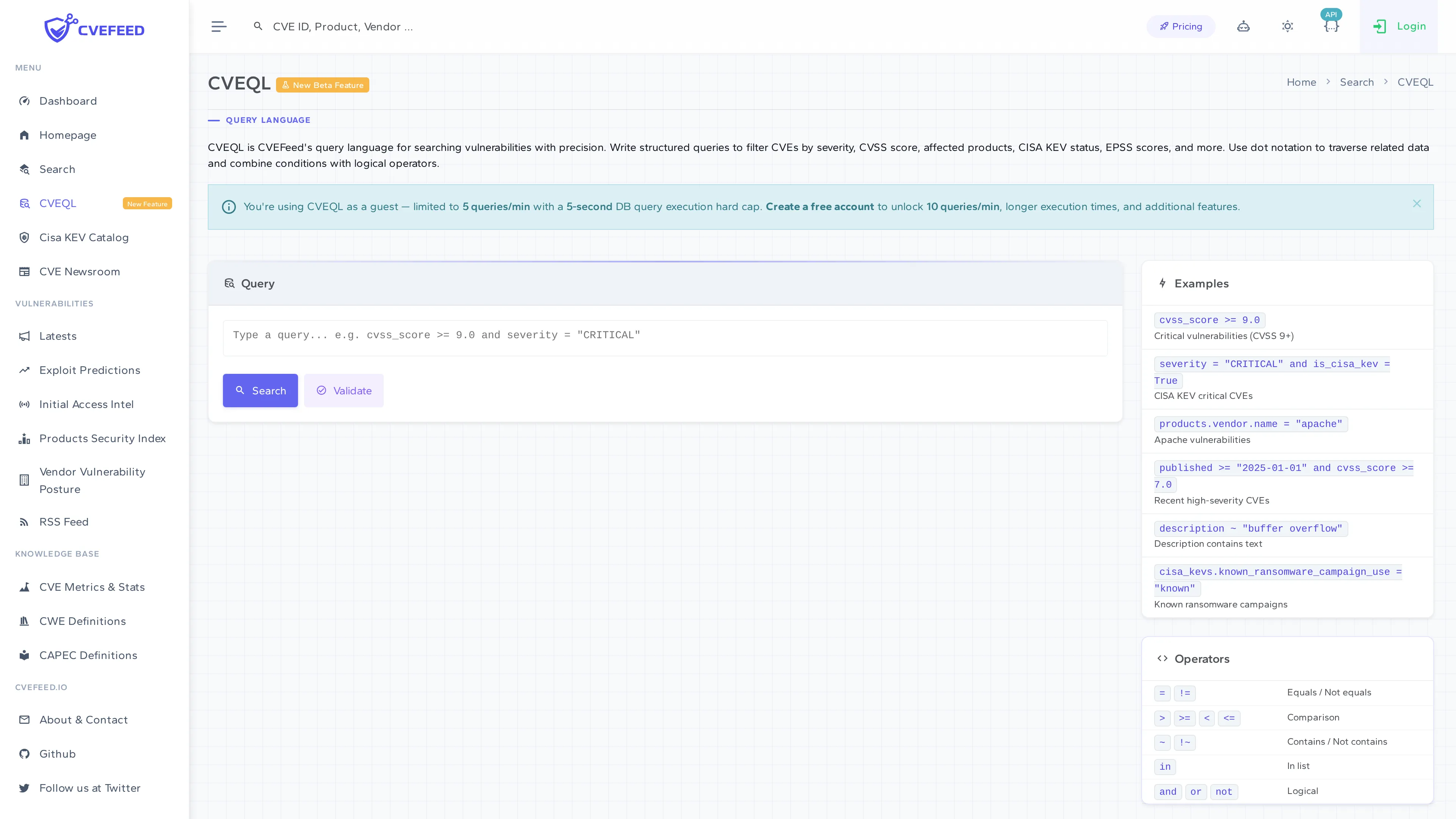
CVEQL — Query Language
CVEQL (CVE Query Language) is CVEFeed.io’s structured query language for searching vulnerabilities with precision. Write queries that combine severity, CVSS score, affected products, CISA KEV status, EPSS scores, and more — using dot notation to traverse related data and logical operators to combine conditions.
CVEQL is available to all users, including unauthenticated guests (with lower rate limits and query timeouts).
Writing Queries
Queries follow the pattern field operator value, combined with and, or, and not logical operators.
Queryable Fields
| Field | Type | Description |
|---|---|---|
id | string | CVE ID (e.g., "CVE-2024-3400") |
description | string | Full vulnerability description text |
published | date | Publication date |
last_modified | date | Last modification date |
status | string | CVE status value |
cvss_score | number | CVSS score (0.0–10.0) |
severity | string | Severity level ("CRITICAL", "HIGH", "MEDIUM", "LOW") |
is_remote | boolean | Whether the vulnerability is remotely exploitable |
is_cisa_kev | boolean | Whether it appears in the CISA KEV catalog |
has_epss | boolean | Whether EPSS scores are available |
has_category | string | Vulnerability category (e.g., "sql_injection", "buffer_overflow") |
Related Data (Dot Notation)
You can query related data using dot notation:
| Field | Description |
|---|---|
products.name | Name of an affected product |
products.vendor | Vendor of an affected product |
cwes.id | CWE identifier |
cwes.name | CWE name |
cisa_kevs.vulnerability_name | CISA KEV vulnerability name |
cisa_kevs.date_added | Date added to CISA KEV |
cisa_kevs.due_date | CISA remediation due date |
cisa_kevs.known_ransomware_campaign_use | Known ransomware campaign usage ("Known", "Unknown") |
epss_scores.score | EPSS probability score |
epss_scores.percentile | EPSS percentile |
Operators
| Operator | Meaning |
|---|---|
= | Equals |
!= | Not equals |
>, >=, <, <= | Numeric/date comparison |
~ | Contains (partial text match) |
!~ | Does not contain |
in | Value is in a list |
not in | Value is not in a list |
after | Date is after |
before | Date is before |
and | Both conditions must match |
or | Either condition must match |
not | Negate a condition |
Example Queries
Critical vulnerabilities with a CVSS score of 9.0 or higher:
cvss_score >= 9.0 and severity = "CRITICAL"CISA KEV critical CVEs:
severity = "CRITICAL" and is_cisa_kev = TrueApache product vulnerabilities:
products.vendor.name ~ "apache"Recent high-severity CVEs from 2025:
published >= "2025-01-01" and cvss_score >= 7.0Vulnerabilities with known ransomware campaigns:
cisa_kevs.known_ransomware_campaign_use = "Known"Buffer overflow vulnerabilities that contain specific text:
description ~ "buffer_overflow"Query Validation
Click the Validate button to check your query syntax without executing it. This helps you catch typos or unsupported field names before running the search.
Rate Limits
CVEQL queries are rate-limited per tier:
| Tier | Queries per Minute |
|---|---|
| Anonymous | 5 (with 5-second query timeout) |
| Free | 10 |
| Starter | 20 |
| Pro | 30 |
| Enterprise | 40 |
Authenticated users get a 10-second query timeout. Unauthenticated queries are automatically filtered to the last 90 days unless a date field is specified in the query.